These are unpredictable times. But that does not mean your business can be put on hold. On the contrary, now is the exact right time to start or accelerate digital transformation. In fact, a recent survey of more than 3,600 small and midsized businesses shows that 51% of SMBs have stepped up their digital transformation investments—and digital transformation is prominent in the plans of 22% of SMBs who report that current crisis has amplified their sense of urgency for an organisation-wide digital transformation.
So you are definitely not alone as you look for ways to power recovery and future growth. To do that, you need intelligent infrastructure to unlock scale through innovation and customer excellence. Because let’s face it, no matter the size of your business, the future belongs to those who use data to differentiate, who understand customers better than anyone else—and who can innovate boldly and quickly.
One piece of the digital transformation puzzle is the need to deploy foundational infrastructure technology that can help you create new market opportunities—faster, cheaper, and more effectively. The way forward? It starts with second-generation hyper-converged infrastructure – HCI 2.0.
First, a brief history of hyper-converged infrastructure
HCI combines server hardware and locally attached storage resources with intelligent software to create flexible building blocks that replace legacy infrastructure. It consists of separate servers, networks, and storage arrays that together enable organizations to take advantage of cloud-like simplicity and scale. You can think about it as an all-in-one appliance that is easy to install and operate.
The first generation of HCI was designed for key jobs and workloads such as data storage, application virtualisation, and application development. The technology allowed businesses to be agile with easily expandable compute, storage and networking resources bundled into a single node. So scaling up infrastructure for things like virtualisation or app development meant just adding another node – and the use of industry-standard hardware reduced over-provisioning and lowered costs.
Now it’s time to take hyper converged even further, faster
In many IT environments today, data is stored and process away from the data center and at the edge. Whether this is surveillance video data for retailers or sensory tags at a manufacturing site, the ability to collect, transcribe, and act on data in real time requires a next-level type of solution. At a time when data drives growth, HPE HCI 2.0 was developed to meet the needs of businesses that need to scale and meet their IT demands today and also 3-to-5 years down the road.
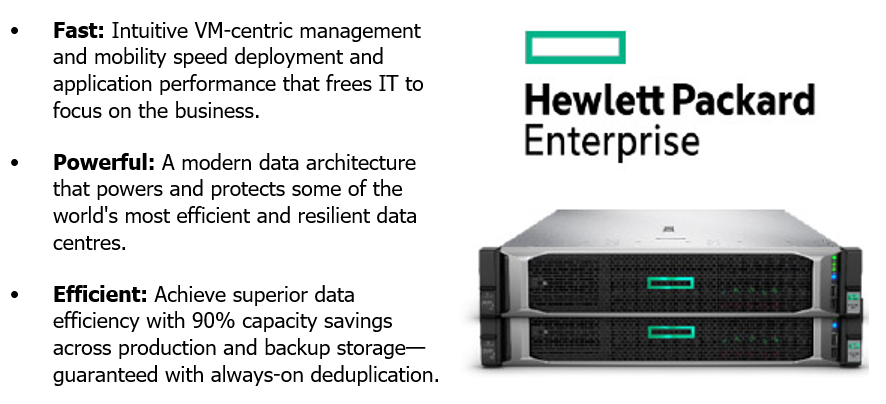
HCI 2.0, exemplified by HPE Nimble Storage dHCI, brings together the best of converged and hyper-converged architectures on a flexible platform with independent scaling of compute and storage. It overcomes the limitations and drawbacks of first-generation HCI with several key innovations.
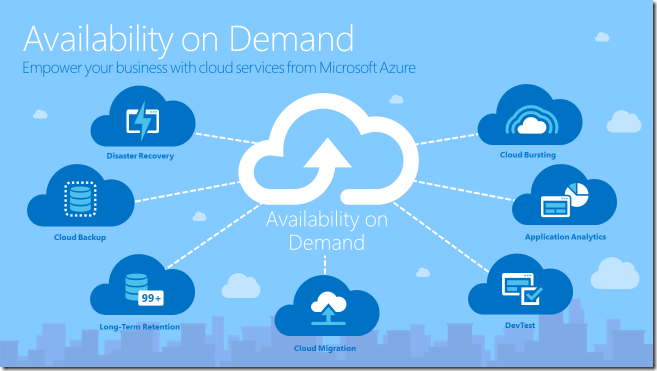
By disaggregating compute and storage resources, HCI 2.0 makes it possible to scale each independently to maximise efficiency. Shared storage that eliminates the network traffic across nodes means low-latency performance with fewer bottlenecks. What’s more, always-on data reduction eliminates tuning and improves performance, while keeping storage dense. And business continuity is assured through advanced replication for multi-site disaster recovery.
Adding intelligence to hyper-converged
HCI 2.0 incorporates HPE InfoSight monitoring tools that use artificial intelligence to predict and prevent disruptions and provide cross-stack analytics that improve application performance and optimise resource use. The simplicity of HCI and the flexibility of a three-tier architecture are now combined with intelligence. This means your organisation can enjoy the benefits of cloud-like architectures without any compromise on performance, availability, or scale.
Put HCI 2.0 to work for your organisation
If your business is in search of:
- Faster time to market—with new opportunities to develop new products and services
- Faster, better user experience—with reduced complexity in IT operations with not tradeoffs or compromises
- Lower costs—derived from using time and skills more efficiently
- Time savings—as businesses respond more quickly and effectively to changing conditions by supporting rapid, no-fuss resource
- Increased productivity—letting predictive analytics help streamline IT operations
Then HCI 2.0 might be the solution for you—one that brings:
- Simple intelligence—automated and on demand, using predictive analytics to quickly diagnose performance problems and identify the root cause so that you don’t have to
- Absolute resilience—designed for 9999% availability of resources, so that even three simultaneous drive failures will not bring the system down
- Efficient scalability—grow compute and storage independently, extended across a hybrid cloud, with industry-leading data efficiency
- Built-in speed—an install time of 15 minutes from rack to apps plus easy administration from one single dashboard
Power into the future
If you’re a small business, consider how HPE HCI 2.0 can help you accelerate scale through innovation—completely free from vendor lock in and free from mundane frustrations. That leaves you with more time to better focus on innovation and how to scale and grow.
If you’re a midsized business, look to HPE HCI 2.0 to deliver meaningful business value and drive greater efficiencies through smoother, reliable IT processes. The stress meter goes down for you too, knowing you have made a smart investment that can improve ROI.
Learn more about our HPE solutions – https://mjf.ie/solution/infrastructure-solutions/